The catalog
Every manual in print, sorted by editorial rating. Filter by section, difficulty, or search the index below.

Applied Cryptography for Backend Engineers
Stop rolling your own, and stop ignoring the ones who did
Bare-Metal C for Modern ARM
Bring-up, linker scripts, and the boot you cannot debug
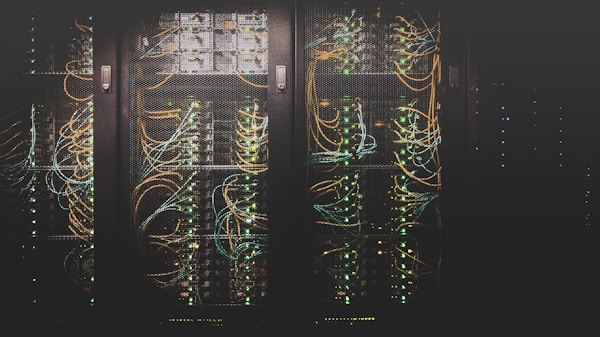
Serving LLMs in Production
GPUs, batching, and the latency budget you forgot about
The Kubernetes On-Call Handbook
Production playbooks for engineers carrying the pager
The Lakehouse Pattern
Iceberg, Delta, and the architecture that replaced your warehouse
Postgres Internals For Operators
MVCC, vacuum, and the planner you cannot ignore

Observability Without Vendor Lock-In
OpenTelemetry, Prometheus, and the cost of every signal

RTOS Internals: FreeRTOS and Zephyr Compared
Schedulers, IPC, and the design choices behind your kernel

Vector Search At Scale
ANN indexes, recall budgets, and the database under your RAG
Consensus In Practice
Raft, Paxos, and the systems engineers ship at 2am

Threat Modeling in Practice
STRIDE, attack trees, and the meeting that prevents the breach

Streaming Pipelines That Survive Outages
Kafka, Flink, and the operational reality of exactly-once